[Archived] AWS IAM (Single Account)
Last updated: December 9, 2025
This article applies only to AWS connections created before July 2025. To check which version you’re using, look at the Domain ID under your domain:
If the domain name shows
aws.amazon.comcontinue with the steps below.
If it shows
aws-iam_ics, proceed with instructions in this article.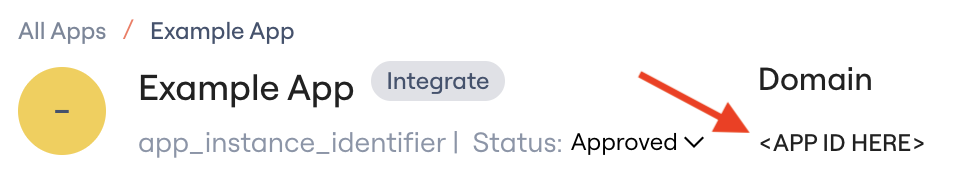
Lumos connects to an individual AWS account by assuming a cross-account IAM role. This enables Lumos to:
Conduct access reviews of IAM users
Monitor role access history via CloudTrail logs
Prerequisites
Elevated AWS IAM permissions
Connection Instructions
Step 1: Create IAM Role for Lumos
Option A: AWS Console
IAM Console → Roles → Create Role
Select Another AWS account → Account ID:
349123981986Enable Require external ID → enter secure value
Attach the following policies:
SecurityAuditAWSCloudTrailReadOnlyAccessA custom policy with the following permissions:
{
"Version": "2012-10-17",
"Statement": [
{
"Effect": "Allow",
"Action": [
"iam:DeactivateMFADevice",
"iam:DeleteAccessKey",
"iam:RemoveUserFromGroup",
"iam:DeleteSigningCertificate",
"iam:DeleteVirtualMFADevice",
"iam:DeleteUserPolicy",
"iam:DeleteSSHPublicKey",
"iam:DeleteUser",
"iam:DetachUserPolicy",
"iam:DeleteServiceSpecificCredential",
"iam:DeleteLoginProfile"
],
"Resource": "*"
}
]
}
Edit the trust relationship:
Set
Principalto:arn:aws:iam::349123981986:user/global-service-account
Set Max session duration to 12 hours.
Copy the role ARN and external ID → paste into Lumos → click Connect.
Option B: Terraform
data "aws_iam_policy" "SecurityAudit" {
arn = "arn:aws:iam::aws:policy/SecurityAudit"
}
data "aws_iam_policy" "CloudTrailReadOnly" {
arn = "arn:aws:iam::aws:policy/AWSCloudTrailReadOnlyAccess"
}
resource "aws_iam_policy" "DeprovisionIAMUser" {
name = "DeprovisionIAMUser"
policy = jsonencode({
Version = "2012-10-17",
Statement = [{
Effect = "Allow",
Action = [
"iam:DeactivateMFADevice",
"iam:DeleteAccessKey",
"iam:RemoveUserFromGroup",
"iam:DeleteSigningCertificate",
"iam:DeleteVirtualMFADevice",
"iam:DeleteUserPolicy",
"iam:DeleteSSHPublicKey",
"iam:DeleteUser",
"iam:DetachUserPolicy",
"iam:DeleteServiceSpecificCredential",
"iam:DeleteLoginProfile"
],
Resource = "*"
}]
})
}
resource "aws_iam_role" "lumos_iam_role" {
name = "LumosSingleAccountIntegrationRole"
max_session_duration = 43200
assume_role_policy = jsonencode({
Version = "2012-10-17",
Statement = [{
Action = "sts:AssumeRole",
Effect = "Allow",
Principal = {
AWS = "arn:aws:iam::349123981986:user/global-service-account"
},
Condition = {
StringEquals = {
"sts:ExternalId" = "CHOOSE_YOUR_EXTERNAL_ID"
}
}
}]
})
}
resource "aws_iam_role_policy_attachment" "attach_security_audit" {
role = aws_iam_role.lumos_iam_role.name
policy_arn = data.aws_iam_policy.SecurityAudit.arn
}
resource "aws_iam_role_policy_attachment" "attach_cloudtrail" {
role = aws_iam_role.lumos_iam_role.name
policy_arn = data.aws_iam_policy.CloudTrailReadOnly.arn
}
resource "aws_iam_role_policy_attachment" "attach_deprovision" {
role = aws_iam_role.lumos_iam_role.name
policy_arn = aws_iam_policy.DeprovisionIAMUser.arn
}